
Government agency attempts to stand its ground against political leader.
- By Ginger Hill
- Dec 05, 2014

Social Security numbers appeared more than 1.1 million times in 601 publicly-posted files stolen by hackers.
- By Matt Holden
- Dec 05, 2014

Wrightstyle, based in the UK, supplies specialist steel and aluminium glazing systems worldwide, and has supplied shopping centres internationally. Jane Embury, the company’s marketing director, looks at retail trickery and the power of light to seduce shoppers.
- By Jane Embury
- Dec 05, 2014
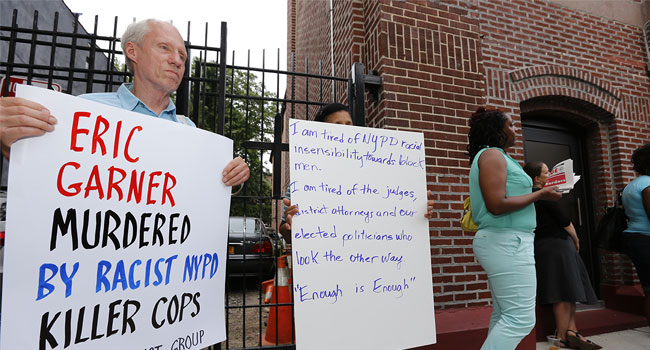
Critics attack NYPD after on social media after "wehearyou Tweet comes out soon after Eric Garner decision.
- By Ginger Hill
- Dec 04, 2014
Ingram Micro awards Bosch with 2014 Smart Partner Award for physical security.

A new report indicates consumers remain concerned about medical technology and the security of their health information and data.
- By Matt Holden
- Dec 04, 2014
Company recognized for foresight and execution in providing convenient way for users to authenticate their online financial interactions.
City of Philadelphia awarded "Most Notable Municipal Security Program, Project or Initiative" as result of partnership.

Stealthy youngster uses ninja-like skills to gain access to his father's iPhone6.
- By Ginger Hill
- Dec 03, 2014
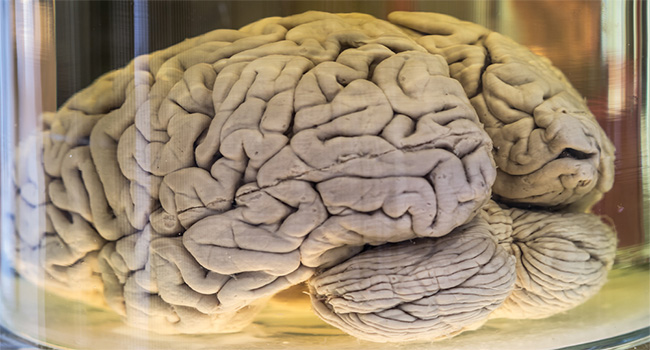
This is roughly half of the specimens the university had in a collection.
- By Matt Holden
- Dec 03, 2014
Demand is growing for high definition and megapixel resolution security cameras because they allow for wider coverage and image detail.
- By Moroni Flake
- Dec 03, 2014
Additional processing capacity enables new advanced vehicle analytics and near-360⁰ ALPR capture on mobile vehicles.
Stratford Square Mall relies on flexibility and image quality of IP video surveillance to maintain safe environments for holiday shoppers and deter theft.
Using only an iPad Mini and the iCrimeFighter app, police eliminate photo cameras, video cameras, audio recorders, notebooks and laptops.
Watch out for cybercriminals looking to make some extra cash during scam season - its a social engineering bonanza with threats on multiple fronts.
SIA Security Market Index surveys select group of nearly 100 executives at SIA member companies to gauge the state of the industry.
Stone Security in Utah finds unique way to increase parent participation in children’s schooling.

Business operations are coming back online after crippling attack.
- By Matt Holden
- Dec 02, 2014